CyberArk Delivers Blueprint for Privileged Access Management Success
February 13 2020 - 8:30AM
Business Wire
Organizations Gain Proven Tools and
Prescriptive Advice for Advancing Cybersecurity Programs and
Enabling Digital Business Priorities
CyberArk (NASDAQ: CYBR), the global leader in privileged access
management, today announced the CyberArk Blueprint for Privileged
Access Management Success. The most comprehensive program of its
kind, CyberArk Blueprint is designed to help customers take a
future-proof, phased and measurable approach to reducing
privilege-related risk.
This press release features multimedia. View
the full release here:
https://www.businesswire.com/news/home/20200213005118/en/
Based on the experience of the CyberArk Labs, Red Team and
incident response engagements, nearly every targeted attack follows
a similar pattern of privileged credential compromise. Those
patterns influenced CyberArk Blueprint’s three guiding principles,
which are foundational to the program: prevent credential theft;
stop lateral and vertical movement; and limit privilege escalation
and abuse.
The CyberArk Blueprint uses a simple, prescriptive approach
based on these guiding principles to reduce risk across five stages
of privileged access management maturity. Customers adopting cloud,
migrating to SaaS, leveraging DevOps and automating with RPA
benefit from being able to prioritize quick wins, progressively
address advanced use cases, and align security controls to digital
transformation efforts across hybrid environments. For example:
- Prevent credential theft: To mitigate internal and
external risks, organizations must first prevent theft of critical
credentials—such as IaaS admins, domain admins or API Keys—that
could be used to conduct network takeover attacks or compromise key
infrastructure accounts. By implementing session isolation, hard
coded credential removal, and theft detection and blocking
strategies, organizations can protect privileged access by humans,
applications and across CI/CD pipelines.
- Stop lateral and vertical movement: To stop threat
actors from pivoting from non-trusted devices to high-value cloud
consoles or domain controllers, this principle focuses on enforcing
credential boundaries, just-in-time access and credential
randomization to break the cyber attack chain.
- Limit privilege escalation and abuse: To stop
adversaries from abusing privileges and to reduce the overall
attack surface, it’s important to implement strong least privilege
controls, behavioral analytics and adaptive response.
CyberArk Blueprint offers templates and custom roadmap design
sessions so organizations of all sizes, including those in both
regulated and non-regulated industries, can progressively expand
privileged access controls and strategy.
“Simple, yet comprehensive, CyberArk Blueprint offers
vendor-neutral guidance that closely aligns privileged access
management initiatives with potential risk reduction, helping
organizations address their greatest liabilities as quickly as
possible,” said Nir Gertner, chief security strategist, CyberArk.
“Regardless of an organization’s privileged access management
maturity, CyberArk Blueprint enables organizations to future-proof
new technology investments while improving security, reducing the
attack surface and driving operational efficiencies.”
To learn more about the CyberArk Blueprint for Privileged Access
Management Success, visit: www.cyberark.com/Blueprint.
Visit CyberArk at RSA Conference (North Expo, Booth #6353) to
learn more about building your blueprint for privileged access
management program success.
About CyberArk CyberArk (NASDAQ: CYBR) is the global
leader in privileged access management, a critical layer of IT
security to protect data, infrastructure and assets across cloud
and hybrid environments and throughout the DevOps pipeline.
CyberArk delivers the industry’s most complete solution to reduce
risk created by privileged credentials and secrets. The company is
trusted by the world’s leading organizations, including more than
50 percent of the Fortune 500, to protect against external
attackers and malicious insiders. A global company, CyberArk is
headquartered in Petach Tikva, Israel, with U.S. headquarters
located in Newton, Mass. The company also has offices throughout
the Americas, EMEA, Asia Pacific and Japan. To learn more about
CyberArk, visit https://www.cyberark.com/, read the CyberArk blogs
or follow on Twitter via @CyberArk, LinkedIn or Facebook.
Copyright © 2020 CyberArk Software. All Rights Reserved. All
other brand names, product names, or trademarks belong to their
respective holders.
View source
version on businesswire.com: https://www.businesswire.com/news/home/20200213005118/en/
Media Relations Contacts: Brian Merrill, fama PR Phone:
+1-617-986-5005 Email: cyberark@famapr.com
Alison Parker, CyberArk Phone: +1-617-663-0162 Email:
press@cyberark.com
Investor Relations Contact: Erica Smith, CyberArk Phone:
+1 617-630-6426 Email: ir@cyberark.com
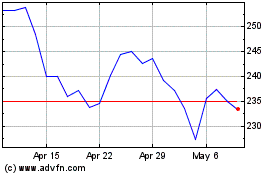
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From Mar 2024 to Apr 2024
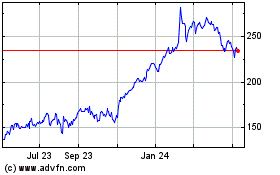
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From Apr 2023 to Apr 2024